Hacking is the activity of finding out about technical details of electronic systems. That is the Science part. Curiosity. The goal is often to use this information in creative and unexpected ways, to do things the original designers of these electronic systems had not planned. That is the Art part.
So, one can be hacker for fun. One can also be hacker for profit. Countries and companies want to eavesdrop on the communications of other countries and companies, maybe disrupt these communications, maybe inject their own messages. But mostly just eavesdrop. This is the job of intelligence agencies.
It is possible to hijack computers, lots of them, and use the resulting army in interesting or profitable ways. Spammers do this.
Detailed knowledge of the ways to break a system is needed to protect it. Computer security firms make a living from such knowledge. System administrators must understand the issues.
Somewat different again is the forensic situation: police has captured some computers or data as part of a criminal investigation, and has to study and understand what it got.
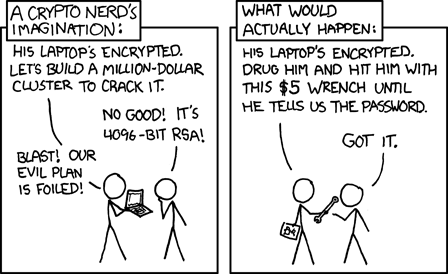
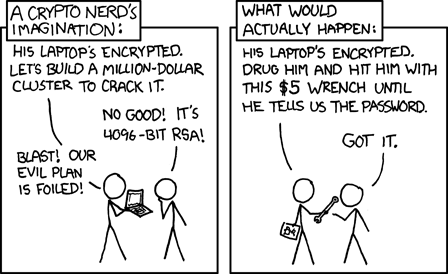
Cryptography is the mathematical discipline that studies how to code and decode secret messages, and how to ensure data integrity and authenticity. It is an important discipline. However, it operates with certain assumptions, on a certain level, and it may be possible to break a cryptographic system without breaking the cryptography.
For example, in mathematics the digital world is modelled as a binary world, with 0s and 1s, and that is also how programmers think about it. But an engineer sees a wave form, and it is said to be possible for example to distinguish on a hard disk a 0 that overwrites a 0 from a 0 that overwrites a 1. But if that is true, then in-place encryption of a file may be less secure than one thought.
Many cases are known where a key logger was planted either in the operating system or directly into the keyboard. Again, this defeats encryption.
More spectacularly, it may be possible to interpret the radiation leaked by the hardware. Maybe a serial line, maybe a display screen. The phenomenon is known as "tempest". Radiation leaked by a display screen is also known as "Van Eck radiation". (Three references: Van Eck and Kuhn & Anderson and Kuhn-2007.)
There is the famous case of the Tenex system, that had a password checking routine that compared the given password with the correct password and returned error when they differed. Sounds reasonable. But the routine returned error as soon as a difference was found. By carefully aligning the string across a page boundary and seeing whether a page fault occurred, it was possible to infer which byte of the password was wrong, and thus, after few attempts, to find the correct password. Again a case where crypto is defeated by working on a different level.